Cloud security compliance
Once a company is in the cloud, it should be concerned with how the cloud provider will help the company remain in compliance with the laws, such as Europe’s General Data Protection Regulation (GDPR) or HIPAA in the U.S. This discussion should start from the very beginning rather than after the cloud service is established.
Securing the cloud is different from securing a traditional data center. The cloud needs to be continuously assessed and automated, which also creates difficulties such as difficulty gaining its visibility and thus achieving compliance. What enterprises need is automated cloud governance. Creative Ground Tech provides six steps to address the pain points.
The Importance of Cloud Compliance
As cloud security adoption has increased, compliance standards have had to evolve, as cloud platforms and services are expected to remain compliant with various international, federal, state, and local security standards, regulations, and laws. A lack of compliance to these rigid rules can lead to legal challenges, penalties, fines, and other negative ramifications.
Cloud compliance and security is more important than ever as the threat landscape becomes more sophisticated. It can’t be overlooked, ignored, or pushed to the proverbial back burner. It’s a topic that must be proactively addressed. But it’s undeniably challenging, which makes it an unattractive endeavor for organizations that already have enough technically complex tasks on their organizational to-do lists.
The first step to gain visibility
We can’t protect what we can’t see, so the first step is to review an enterprise’s cloud environment to understand its workloads, configurations, and processes. Businesses that want to avoid falling victim to security threats and increasing operational costs should build a comprehensive and comprehensive view of the network to eliminate visibility gaps by maintaining a flexible, secure digital environment for innovation and growth.
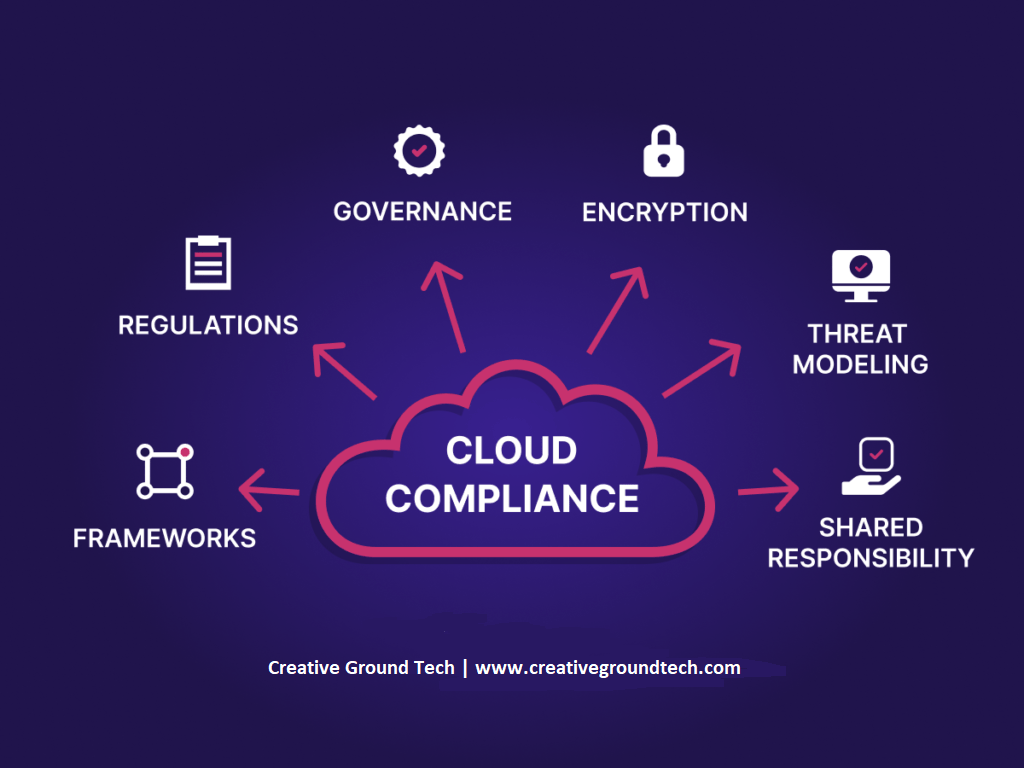
Step 2: Select the compliance framework and scope
After assessing the security posture of the cloud environment, the enterprise can conduct a high-level compliance program and select the appropriate compliance framework and scope. Different industries have different regulatory requirements, such as ISO27001, PCI DSS, SOC2, and GDPR. After choosing the relevant framework, the enterprise can assess which cloud assets/accounts are handling sensitive information etc.
Step 3: Assess Initial Results and Plans
Depending on the chosen framework and scope, companies can gain an initial understanding of the current security situation to build an automated security compliance system. Businesses should reduce irrelevant automated alerts and focus on adding custom security compliance rules to automated systems to meet business-specific needs.
Step 4 Continuously monitor cloud security compliance
Ad hoc security assessments are unrealistic, and enterprises need to carry out continuous monitoring and remediation plans for cloud security compliance, and need to determine the frequency of reporting feedback and determine who will take action in response to the report.
Step 5 Automated Repair
Automatic remediation is essential, rather than relying solely on humans, which can greatly reduce the time to resolve security issues. By automatically applying security policies or changing configurations, businesses can easily spot misconfigured resources, and automation can quickly fix many critical issues.
Step 6 Reporting and Auditing
To ensure ongoing industry certification, businesses need to be able to generate security compliance reports at any given time. Enterprise automation tools should be able to provide snapshots on demand and generate a timeline of security posture over time.
While every organization is different, the need for proper security solutions is a shared concern. Contact Creative Ground Tech today to learn more about our products and solutions – including our security consulting service, which can help businesses like yours as you figure out what it looks like to remain compliant in such a dynamic ecosystem.